On May 25, 2018, the new and considerably more onerous general data protection regulations take effect. It affects all companies managing personal information originating from countries within the European Union (EU). As the fines for non-compliance are eye-watering, and the potential ‘ethical fallout’ highly damaging, a successful GDPR project is an essential risk mitigation tool.
What is the GDPR?
The General Data Protection Regulation (GDPR) is a data protection regime set up to increase individuals’ rights regarding their personal information (PI). It has placed a much larger emphasis and obligation on the companies that use this information, with individuals now controlling how their data can be processed, being able to demand a copy of what is being held or even being able to demand that their records be expunged.
Key terms you need to know
So GDPR is a regulation presiding over the protection of controlling and processing personal information. It is applicable to all companies globally that perform the roles of a Controller or Processor of personal data pertaining to EU citizens. Therefore, defining exactly what the below terms mean is essential in achieving compliance.
Protection
 The rights of the individual start at the point of consent to use their data. The article, “Top UK firms’ websites violate key GDPR principles,“ states very succinctly that companies are required to “state clearly at the point of capture how they will use an individual’s data. Permission to use their data must be explicit and demonstrated through an action such as ticking a box.”
The rights of the individual start at the point of consent to use their data. The article, “Top UK firms’ websites violate key GDPR principles,“ states very succinctly that companies are required to “state clearly at the point of capture how they will use an individual’s data. Permission to use their data must be explicit and demonstrated through an action such as ticking a box.”
But protection is about more than just consent, as it now includes rights to be informed, the right of access, the right to rectification, the right to erasure, the right to restrict processing, the right to data portability, the right to object and the right not to be subject to automated decision-making including profiling.
Processing
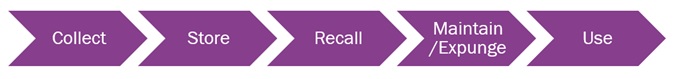
This includes all actions prevalent throughout the conduct of an end-to-end PI process lifecycle such as the one outlined below. As such, it includes any operation performed upon personal data or sets of personal data.
 There are two distinct roles in this process which require definition as they each carry different obligations under GDPR:
There are two distinct roles in this process which require definition as they each carry different obligations under GDPR:
Controller: A Controller is a person(s) who determines the purposes and means of the processing personal data. They are the people responsible and obligated for compliance with the regulation.
Processor: A Processor is a legal person who processes personal information on behalf of the Controller.
Personal information
According to international law firm White and Case, in their article, “Key definitions – unlocking the EU GDPR,” personal information now has a broader definition than previously used and includes all information relating to an identifiable natural person either directly or indirectly. That means not only name, number, email address, occupation, etc., but also online identifiers such as cookie strings, IP addresses and mobile device IDs as further outlined by European law firm Fieldfisher in their blog, “Getting to know the GDPR.”
European citizens
The term European citizens is defined in this context as the citizens of the 28 nations forming the EU, including those from nations in the European Economic Area (EEA): Norway, Iceland, Lichtenstein and Switzerland, which is neither in the EU or EEA but is part of the single market (Source: UK government website).
What are the implications?
Financial implications
The Information Commissioner’s Office (ICO) will be able to impose fines of €20m (£17m) or up to 4% of global annual turnover, whichever is the greater, for businesses who breach the regulations. As the ICO need to fund its operation via these fines, it seems inevitable that fines will be imposed as soon as the legislation is in force.
Ethical implications
More and more, breaches of data privacy laws, and in particular, security breaches leading to the dissemination of personal information, are considered breaches of ethics leading to stakeholder responses appropriate to such an event.
Legal implications
There should be an identifiable legal basis upon which the processing of PI under GDPR should be documented and enabled, and satisfaction of an express legal requirement under the term “data protection by design and by default.” In certain circumstances, privacy impact assessments (PIAs) – referred to as “Data Protection Impact Assessments” or DPIAs – are mandatory. In certain circumstances, a Data Protection Officer (DPO) must be designated. This ICO document on preparing for the GDPR holds a lot more information on this subject.
Operational implications
Personal information as described above should be collected with compliant consent, and legacy data which is processed by a company should have specific consent registered against it, and policies and procedures in places to ensure processing matches consent.  Processes should be compliant with the “data protection by design and default” concept.
Processes should be compliant with the “data protection by design and default” concept.
Data breach procedures should be in place to allow the detection, report and investigation of a personal data breach and subject access request procedures should be in place to comply with the new one-month timeframe.
What actions should you be taking now?
Almost a quarter of UK and US firms are likely to miss the GDPR deadline, according to a report on ComputerWeekly.com, placing them at risk of non-compliance and exposed to the implications outlined above. But by carrying out these four steps, you could be well under way to being compliant.
1. Set up a specific project/program
If you have not already done so, it would be advisable to set up a data privacy program or at least a GDPR project team. This blog on CFO.com entitled, “The financial case for a data privacy program,” provides useful guidance to assist in the project start-up. The key aspects of this project are that it should be sponsored from the top of the organization, be sufficiently funded and have in place the governance for escalation and decision-making.
2. Education
You will be asking all Controllers and Processors to audit their data and procedures to enable compliance. Training these people on the importance and specifics of GDPR compliance will speed up the process and reduce the risk of breaches in future. It is both a key aspect in achieving quality processes and the change management implicit in programs such as these. Providing mandatory education programs should be an early and engaging output from the project team.
3. Data and process audits
Locate existing PI data and the qualities of the data and processes that surround it as a discovery exercise. It should highlight whether existing data is compliant and whether existing processes allow for compliance. A data and process owner should be identified and any non-compliance gaps fully documented with a fully costed and resourced plan in place to allow corrections. All plans should have the backing of the project team.
4. Systems and process changes
Undertaking the exercise to close all non-compliance gaps using the plans may require new or updated processes, new or updated application solutions and new or updated roles. Depending on the size of the non-compliance gaps, it may also require temporary roles to backfill whilst the exercise is being completed.
GDPR comes into force on May 25, 2018. It is a regulation presiding over the protection of controlling and processing personal information. The significance of non-compliance is severe and wide-ranging. Nearly a quarter of companies are currently at risk of non-compliance as they have no project in place to deal it. Using the four steps above reduces this risk considerably.
I have included below some useful links to help you on your journey and I would love to hear from you if you have any questions or concerns in relation to GDPR.
Readiness assessment from the ICO
Opportunities to be gained from GDPR
I welcome comments on this or any other topic concerning finance, HCM, CSR and business strategy.
Connect, discuss, and explore using any of the following means:
- Twitter: @stevetreagust
- Email: steve.treagust@ifsworld.com
- Blog: http://blog.ifs.com/author/steve-treagust
- LinkedIn: https://www.linkedin.com/in/stevetreagust
Do you have questions or comments about GDPR compliance?
We’d love to hear them so please leave us a message below.
geometry dash
It would be advisable to set up a data privacy program or at least a GDPR project team
click
Really like this great article here.
trending stories
I don’t think so, it was a matter before which we can’t deal easily but now it’s easy to handle.
Suprabha
Hi Steve Treagust, Nice Article. I really impressed with it because I know lots of things from your General Data Protection Regulation (GDPR) Article. Thanks for sharing and pleas keep writing there type of articles.